Outsourced IT – the order processing contract for your protection
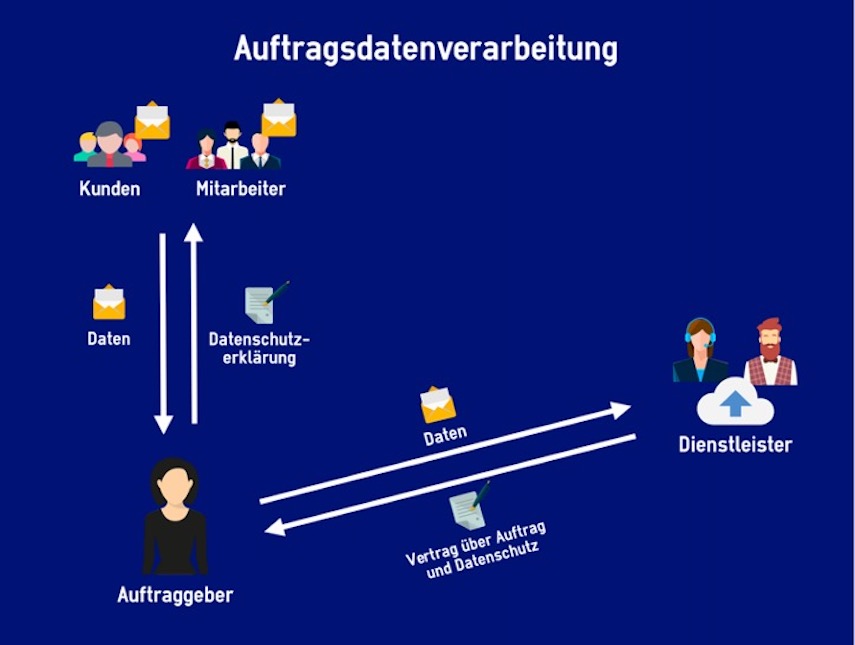
Outsourced IT – the order processing contract for your protection The media report on cyber incidents every day, as the victims become more prominent and more numerous. Many companies are increasingly aware that they need to invest more in IT security. At the same time, many are relying on their system house to take care […]
Outsourced IT – the data processing agreement to protect you

Outsourced IT – the data processing agreement to protect you The media reports daily on cyber incidents, as the victims become more prominent and numerous. In many companies, the realization is growing that more needs to be invested in IT security. Many rely on their supervising system house, according to the motto “they will make […]
How and why data protection law is so relevant and helps to protect our privacy
How do we protect our data in the machine-driven age? Shermin Voshmgir, Business Informatics, University of Heidelberg, 2018, emphasizes the necessity of data protection law in her lecture by casually drawing attention to one of the central requirements, namely “Privacy by Design”: Devices, applications, information systems, etc. must be designed during their technical development to […]
How and why the Data Protection Act is so relevant and helps protect our privacy
How do we protect our data in the machine-driven age? Shermin Voshmgir, Business Informatics, University of Heidelberg, 2018, underlines the necessity of the Data Protection Act in her presentation by casually drawing attention to one of the central requirements, namely “Privacy by Design”: devices, applications, information systems, etc., must be designed already during their technical […]
